Latest blog articles
-
“The SolarWinds Attack is, to date, the most visible, widespread, and intrusive information technology (‘IT’) software supply chain attack – i.e., a cyber attack that corrupts IT software and uses that software as an attack vector. Supply chain attacks are dangerous because the malware is embedded...
-
Over the last 20 years, access to cheap computational capacity has increasingly led to the harvesting of more and more personal data, without having to worry too much about costs related to data storage and processing activities.
-
What was promised by the GDPR (Art. 80 and Rec. 142) is now a reality!
-
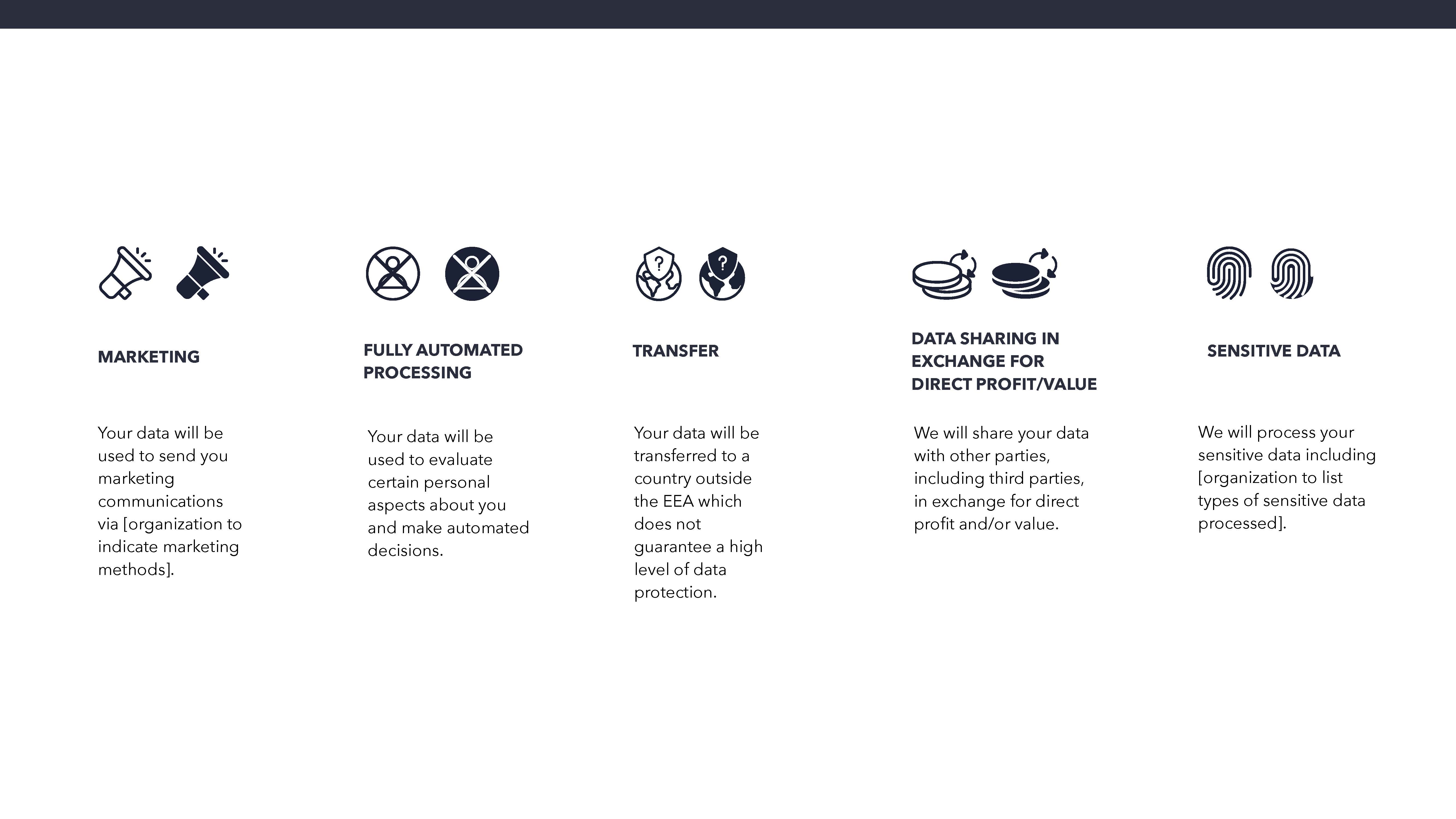
Survey on the Maastricht University Data Protection as a Corporate Social Responsibility (UM DPCSR) Icons Version 1.0 to facilitate users’ understanding of how their data is used.
-
Constructing a functioning single market for business and trade among the Member States of the European Union (EU) has been the cornerstone of the EU project, and remains one of the strongest drivers for EU-level legislative reform. Over the years, the EU has prioritized the harmonization of...
-
There has been substantial political debate over the last decade about the role of experts in policymaking. But how are these trends likely to develop in future? Drawing on a new edited volume, Vigjilenca Abazi, Johan Adriaensen and Thomas Christiansen set out four distinct scenarios concerning the...
-
Recent days have seen the meteoric rise and fall of the European Super League (ESL). This new league would have consisted of 15 founding clubs and 5 other clubs; the former consisting of ‘big clubs’ which could not be relegated and the latter in clubs who performed well over the past years on a...
-
Automated decision-making (‘ADM’) systems are algorithm decision-making tools, which issue either a partial or a full decision. While their use by national public administration is no new phenomenon, the European Union (‘EU’) has now also embraced this novel method of administrative decision-making.
-
Thank God for Judge Egidijus Kūris. In ECtHR ruling Ahmet Hüsrev Altan v. Turkey of 13 April, he showed that decontextualized analysis is not inherent to supranational judicial review. Once again saucing up his dissent with Bob Dylan, he asked “how many times can [the ECtHR] turn [its] head and...
-
When we think of cybersecurity we are generally concerned with the code, algorithms and systems that are responsible for the functioning of out digital technologies and the safety of our sensitive data. What has become increasingly apparent is the role of humans in ensuring the security of our...