Latest blog articles
-
-
-
Questions surrounding how the EU budget is spent or audited have been, and will always be, of interest to EU citizens. Formally, the responsibility for the implementation of the budget rests with the Commission, but it is well known that the Member States have a crucial role to play, especially in...
-
Breath in, breath out. Yes, the judgment of the (unlawfully composed) Polish Constitutional Tribunal is a serious challenge to the European Union’s legal system and to the principle of primacy of EU law. No, Poland has not activated the process of withdrawal from the EU under Article 50 TEU. Yes, EU...
-
This blog post is a re-elaboration of my interview this morning with Luca Bertuzzi, Digital & Media Editor from EurActiv, available here.
-
“The SolarWinds Attack is, to date, the most visible, widespread, and intrusive information technology (‘IT’) software supply chain attack – i.e., a cyber attack that corrupts IT software and uses that software as an attack vector. Supply chain attacks are dangerous because the malware is embedded...
-
Over the last 20 years, access to cheap computational capacity has increasingly led to the harvesting of more and more personal data, without having to worry too much about costs related to data storage and processing activities.
-
What was promised by the GDPR (Art. 80 and Rec. 142) is now a reality!
-
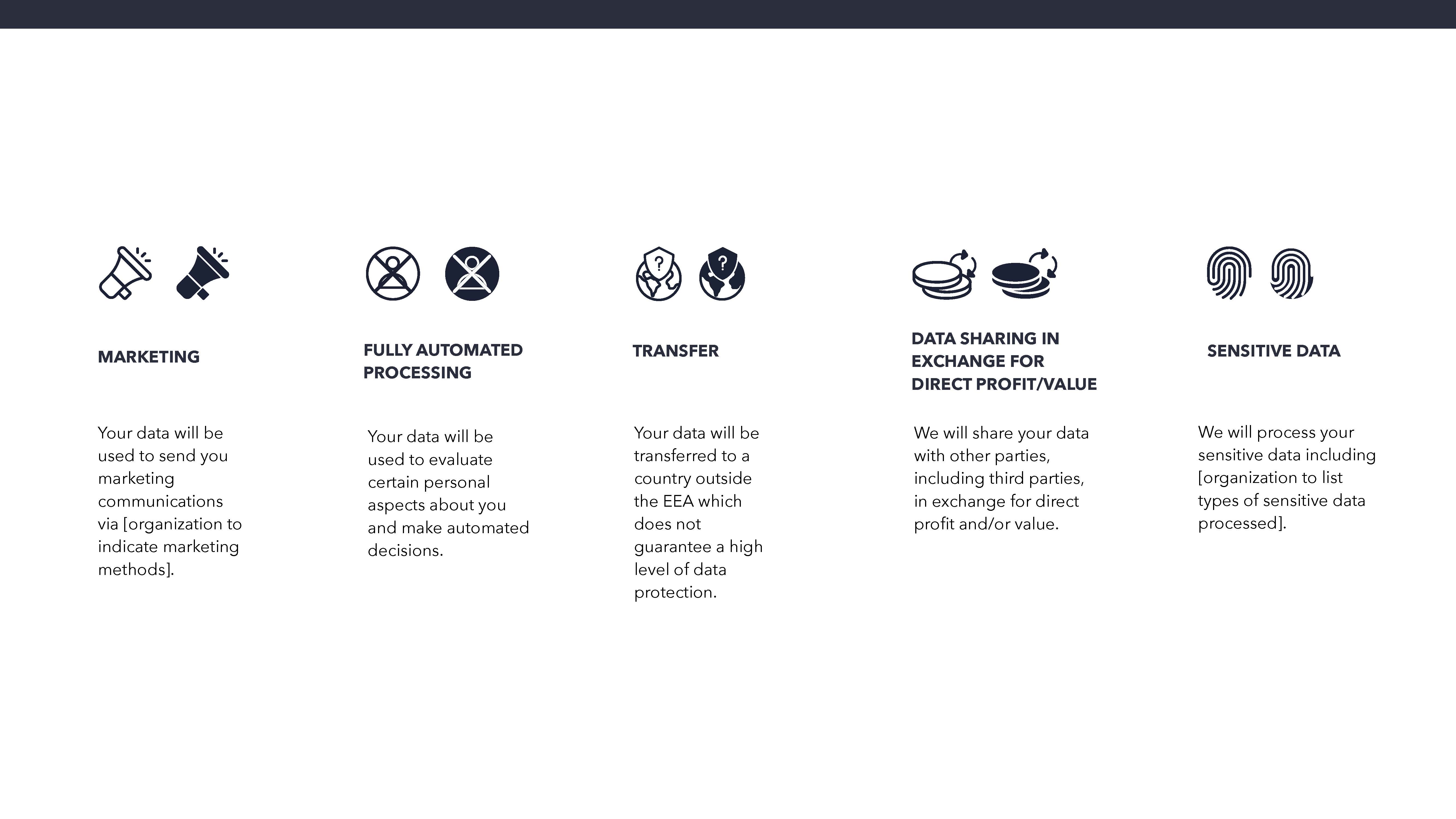
Survey on the Maastricht University Data Protection as a Corporate Social Responsibility (UM DPCSR) Icons Version 1.0 to facilitate users’ understanding of how their data is used.
-
Telegram is a powerful tool for end-to-end encrypted communication and one of the most popular messenger apps in Russia. However, one aspect often evades public attention: Telegram is swamped with bots which gather and disseminate personal data.