Latest blog articles
-
The IMCO Committee is trying to amend the Unfair Commercial Practices Directive (2005/29) to include a ban on dark patterns. The proposed amendments are part of the EU’s plans to empower consumers for the green transition and the Parliament is expected to address the proposed amendments on 17 April...
-
Over the weekend of March 25-26, TikTok users started sharing videos of their experiences trying to delete their Instagram accounts on Android devices. Users took issue with not being able to delete their accounts via the Instagram app and having to use a desktop/mobile browser to complete the...
-
In this piece, I will use two memes to begin to unpack what I think is the common denominator of contemporary populist rhetoric. I will explain that the real substance of this rhetoric is the creation of a false moral equivalence, revealing a nihilism. Finally, I will suggest how this false moral...
-
A male senior manager enthusiastically slapping a female colleague’s buttocks – is that acceptable? And what if a female staff member did this to her female supervisor? Or a manager who puts his arm around a colleague who is having a hard time? What is crossing the line? Who decides?
-
I am very pleased that today we will start teaching the EU and Global Cybersecurity Fundamentals course within the Advanced Master in Privacy, Cybersecurity and Data Management LLM we created at ECPC. Today we will kick off the course with Brian Honan, who will lecture on the concept of...
-
This blog post is a re-elaboration of my interview this morning with Luca Bertuzzi, Digital & Media Editor from EurActiv, available here.
-
“The SolarWinds Attack is, to date, the most visible, widespread, and intrusive information technology (‘IT’) software supply chain attack – i.e., a cyber attack that corrupts IT software and uses that software as an attack vector. Supply chain attacks are dangerous because the malware is embedded...
-
Over the last 20 years, access to cheap computational capacity has increasingly led to the harvesting of more and more personal data, without having to worry too much about costs related to data storage and processing activities.
-
What was promised by the GDPR (Art. 80 and Rec. 142) is now a reality!
-
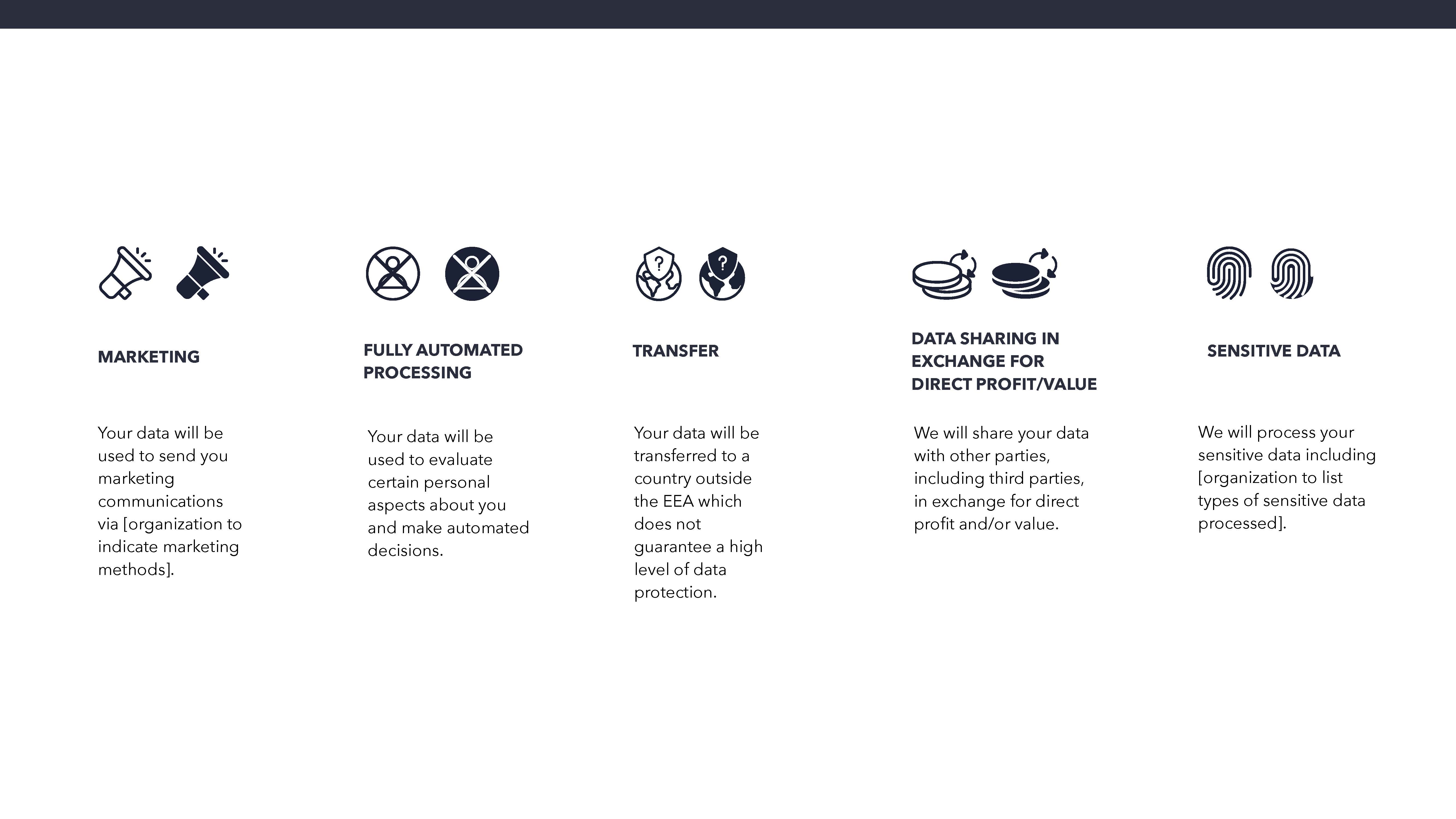
Survey on the Maastricht University Data Protection as a Corporate Social Responsibility (UM DPCSR) Icons Version 1.0 to facilitate users’ understanding of how their data is used.