Latest blog articles
-
This blog post is a re-elaboration of my interview this morning with Luca Bertuzzi, Digital & Media Editor from EurActiv, available here.
-
“The SolarWinds Attack is, to date, the most visible, widespread, and intrusive information technology (‘IT’) software supply chain attack – i.e., a cyber attack that corrupts IT software and uses that software as an attack vector. Supply chain attacks are dangerous because the malware is embedded...
-
Over the last 20 years, access to cheap computational capacity has increasingly led to the harvesting of more and more personal data, without having to worry too much about costs related to data storage and processing activities.
-
What was promised by the GDPR (Art. 80 and Rec. 142) is now a reality!
-
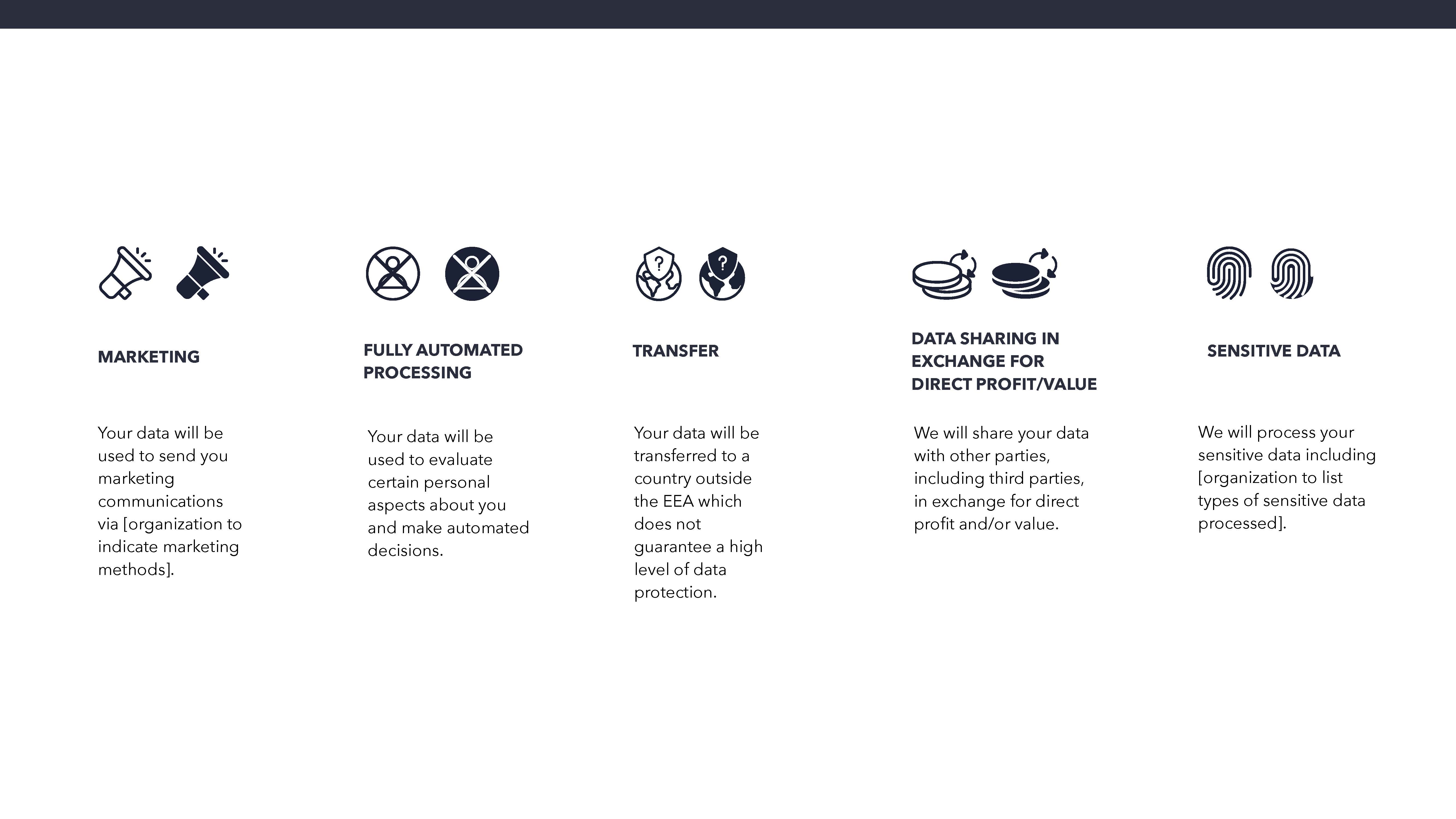
Survey on the Maastricht University Data Protection as a Corporate Social Responsibility (UM DPCSR) Icons Version 1.0 to facilitate users’ understanding of how their data is used.
-
Over the past twelve months we have been working to finalize the Maastricht University Data Protection as a Corporate Social Responsibility Framework (see our first Manifesto). An important aim of the forthcoming Framework is found in the internationally recognized principle of transparency. One of...
-
The Swedish Data Protection Authority recently launched an investigation into Umeå University’s handling of sensitive personal data, specifically data obtained from the Danish Police Authority for research purposes.
-
I think that today is a good day to ask the future Members of the European Parliament and American Presidential Candidates to think about a global dimension of data protection and to commit themselves to develop international legislative instruments that have the power to truly enable world-wide...
-
On 6 November 2018 the ICO published it’s report to Parliament (Investigation into the use of data analytics in political campaigns A report to Parliament 6 November 2018).
-
Legal compliance = primary enabler of Smart Data and Data protection by design and by default. We return to the vitality of compliance with data protection principles, the ultimate objective which can be successfully achieved through the correct application of the data protection by design approach...