Latest blog articles
-
How does EU consumer laws address dark patterns on the Internet? This topic has been part of the scholarly debate during the panel discussion “The AI-assisted consumer”, organized on 6 December 2022 in collaboration with Glaw-Net and IGIR.
-
The widespread use of AI-assisted technologies in the digital sphere has given rise to the concept of digital vulnerability, as a contextual vulnerability experienced by internet users. This phenomenon sparks debate about whether the current legislative framework is sufficient to ensure effective...
-
-
Questions surrounding how the EU budget is spent or audited have been, and will always be, of interest to EU citizens. Formally, the responsibility for the implementation of the budget rests with the Commission, but it is well known that the Member States have a crucial role to play, especially in...
-
This blog post is a re-elaboration of my interview this morning with Luca Bertuzzi, Digital & Media Editor from EurActiv, available here.
-
Over the last 20 years, access to cheap computational capacity has increasingly led to the harvesting of more and more personal data, without having to worry too much about costs related to data storage and processing activities.
-
What was promised by the GDPR (Art. 80 and Rec. 142) is now a reality!
-
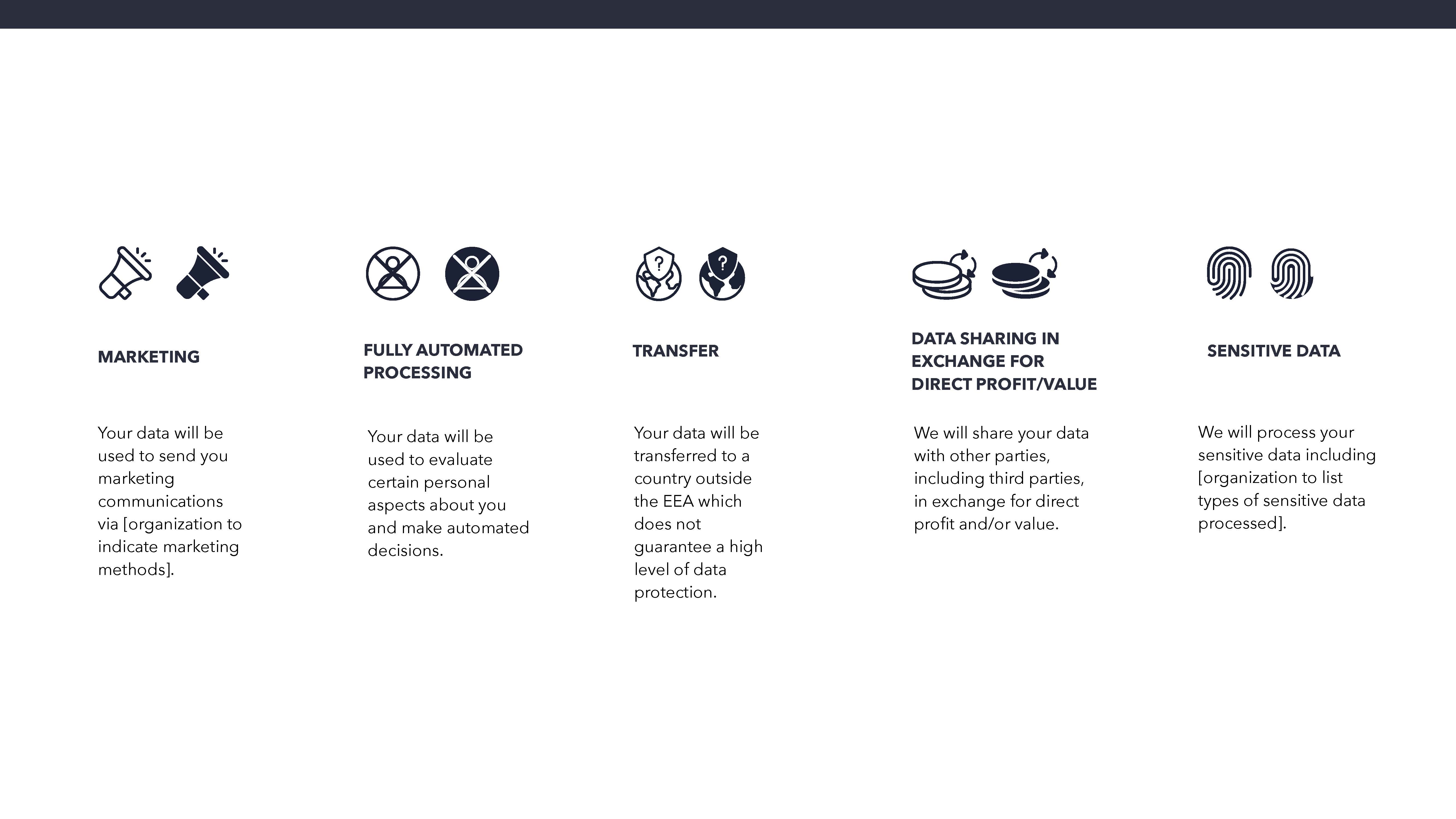
Survey on the Maastricht University Data Protection as a Corporate Social Responsibility (UM DPCSR) Icons Version 1.0 to facilitate users’ understanding of how their data is used.
-
When we think of cybersecurity we are generally concerned with the code, algorithms and systems that are responsible for the functioning of out digital technologies and the safety of our sensitive data. What has become increasingly apparent is the role of humans in ensuring the security of our...
-
Telegram is a powerful tool for end-to-end encrypted communication and one of the most popular messenger apps in Russia. However, one aspect often evades public attention: Telegram is swamped with bots which gather and disseminate personal data.