Latest blog articles
-
I am very pleased that today we will start teaching the EU and Global Cybersecurity Fundamentals course within the Advanced Master in Privacy, Cybersecurity and Data Management LLM we created at ECPC. Today we will kick off the course with Brian Honan, who will lecture on the concept of...
-
This blog post is a re-elaboration of my interview this morning with Luca Bertuzzi, Digital & Media Editor from EurActiv, available here.
-
“The SolarWinds Attack is, to date, the most visible, widespread, and intrusive information technology (‘IT’) software supply chain attack – i.e., a cyber attack that corrupts IT software and uses that software as an attack vector. Supply chain attacks are dangerous because the malware is embedded...
-
Over the last 20 years, access to cheap computational capacity has increasingly led to the harvesting of more and more personal data, without having to worry too much about costs related to data storage and processing activities.
-
What was promised by the GDPR (Art. 80 and Rec. 142) is now a reality!
-
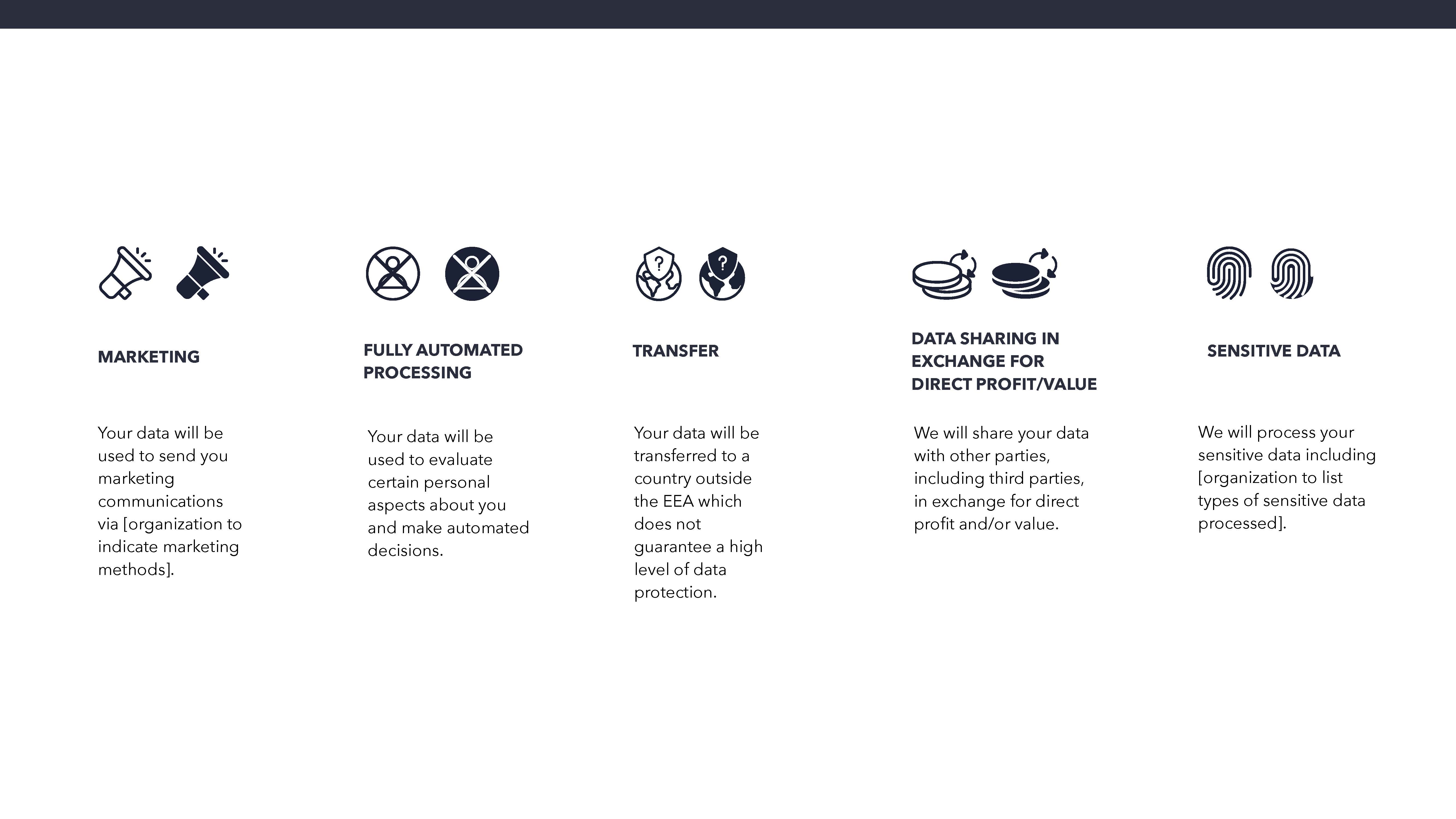
Survey on the Maastricht University Data Protection as a Corporate Social Responsibility (UM DPCSR) Icons Version 1.0 to facilitate users’ understanding of how their data is used.
-
28 January was Data Protection Day, an annual celebration of privacy and data protection commemorating the date that Convention 108 of the Council of Europe was first opened for signature. This year, however, I would invite all data protection practitioners, academics, business leaders, educators...
-
Over the past twelve months we have been working to finalize the Maastricht University Data Protection as a Corporate Social Responsibility Framework (see our first Manifesto). An important aim of the forthcoming Framework is found in the internationally recognized principle of transparency. One of...
-
Since the educational spaces in our faculty have all been named, we would like to tell about the background of the elected jurists and cases. Through a series of blogs we want to make the names come to life and show that our building houses a legal faculty. After all, not everyone knows all the ins...
-
In the evolving COVID-19 scenario in which business continuity also depends on adequate data protection and cybersecurity practices on the part of organizations, knowledge mapping of privacy & data protection guidance and cybersecurity best practices has taken on an even more important role.